Technology News
Nokia Caught Wiretapping Encrypted Traffic From Its Handsets

In 2013 Nokia found using proxy server for transferring user data .
Security researcher Gaurang Pandya posted an article in December about some unexpected behavior with their Nokia handset. It would appear that the browser traffic from the handset would get diverted through Nokia’s servers.
Then, a followup article on January 9 dropped the bomb, and the article goes into quite technical detail: It wasn’t enough that Nokia diverted all traffic from its handsets through its own servers, it also decrypted the encrypted traffic, re-encrypting it before passing it on, issuing HTTPS certificates on the fly that the Nokia phone has been instructed to trust as secure.

Nokia, the cellphone manufacturer, has been listening in to all encrypted communications from its handset’s browser. Every connection advertised as secure – banking, social networks, dating, corporate secrets – has been covertly wiretapped by Nokia themselves and decrypted for analysis.
This means that Nokia has deliberately been wiretapping all traffic that has been advertised as encrypted on these Nokia handsets – including but not limited to banking, dating, credit card numbers, and corporate secrets – and looking at your secrets in cleartext.
This means that Nokia puts itself between your bank and you, and presents itself as YourBank, Inc. to your phone. This wouldn’t normally be possible, if it weren’t for the fact that the phone had been specifically designed for this deceptive behavior, by installing a Nokia signing certificate on the phone
From the post :
After discovering that HTTP traffic from the phone is getting redirected through Nokia’s server farm as shown in previous post, the most obvious next step was to check if at least HTTPS traffic is getting its due respect and is being transferred without any intermediate host inspecting it. Due to fact that HTTPS traffic is encrypted before getting transmitted, it is not possible to look at HTTP(S) packet header in order to figure out details as was done in case of HTTP as per previous post. However there are two ways to get an idea of how traffic is flowing.
- Check if DNS requests are sent for requested website.
- Check certificate sent from server
DNS Request Check
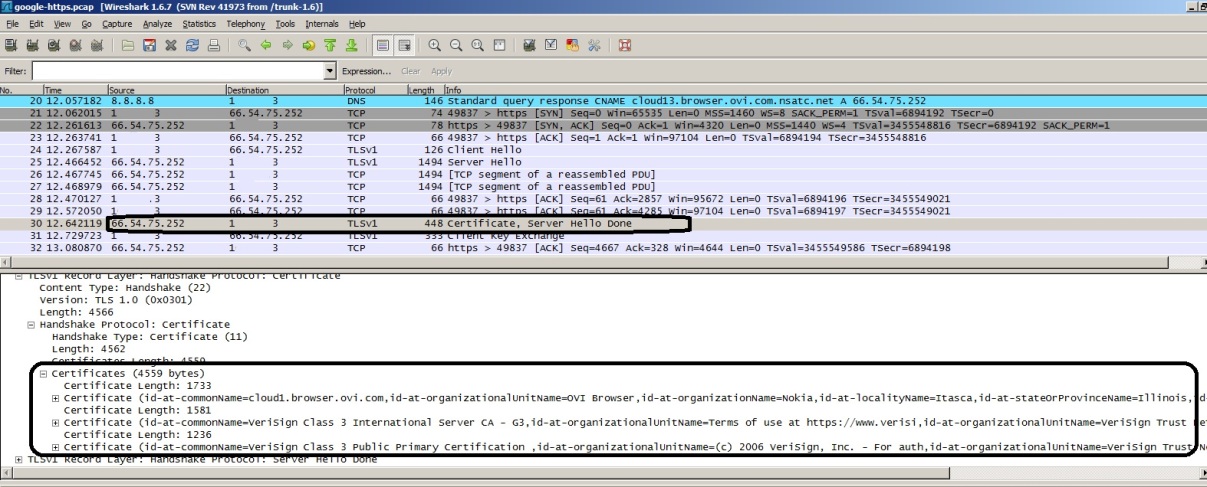
The goal of this test was to find whether the phone is sending DNS query for site that is being requested to be browsed. To test this we had browsed site https://www.google.com through Nokia browser. Ideally the phone should have send DNS query requesting IP address for “www.google.com”, which would have looked normal. On the contrary when checked, the DNS request was sent for “cloud13.browser.ovi.com” which is same host where we had seen even HTTP traffic being sent as per previous post. Not just that, there was no attempt made to resolve “www.google.com”. The wireshark snapshot given below proves this fact, but there is no way from wireshark snapshot taken off wifi router it can be proved that the request was originally made for https://www.google.com and not for cloud13.browser.ovi.com.
Certificate Response Check
It is evident from above snapshot, that even https requests are also getting redirected to Nokia/Ovi servers, which raises a question about certificate that it being received from Nokia’s servers and trusted list of certificates in Nokia phone in subject. Let us first look at certificates being received from Nokia servers during this transaction. Given below is packet sniff from wifi router.
When checked trusted certificates in phone it is found that Nokia has pre-configured the phone by trusting at least one of these certificates, which is the reason why there are no security alerts being shown during this Man In The Middle (MITM) attack by Nokia. The snapshot given below shows details about each of the three certificates that are shown in packet capture.
One more thing that should be noticed here is that the DNS request was send for “cloud13.browser.ovi.com” where as certificate (middle one) says it was issued to “cloud1.browser.ovi.com”, and still there was no security warning thrown on the phone.
Conclusion
From the tests that were preformed, it is evident that Nokia is performing Man In The Middle Attack for sensitive HTTPS traffic originated from their phone and hence they do have access to clear text information which could include user credentials to various sites such as social networking, banking, credit card information or anything that is sensitive in nature. In short, be it HTTP or HTTPS site when browsed through the phone in subject, Nokia has complete information unencrypted (in clear text format) available to them for them to use or abuse. Up on checking privacy statement in Nokia’s website following can be found.
Websites accessed The URLs of such sites which you access with the Nokia Browser are stored by Nokia. However, we will not collect any personally identifiable information in the context of providing the service. Your browsing is not associated to any personally identifiable information and we do not collect any usernames or passwords or any related information on your purchase transactions, such as your credit card number during your browsing sessions. Also, additional parameters in the URL are not stored.
For additional information on their privacy policy you may want to visit their Privacy Policy Page or Nokia Browser Privacy Policy Page
Update of 10th January,2013
Just noticed when I tried to browse a site through Nokia browser, I got a message to upgrade browser. I clicked remind later as I wanted to something. My guess is Nokia would have fixed this. But nothing can be said without actually upgrading and testing. Also seeing “Update your browser” in browser.nokia.com. Since no date/time stamp is given there it can not be confirmed if this is new or old.
Update of 11th January,2013
Just upgraded my Nokia browser, the version now is 2.3.0.0.48, and as expected there is a change in HTTPS behaviour. There is a good news and a bad news. The good news is with this browser, they are no more doing Man-In-The-Middle attack on HTTPS traffic, which was originally the issue, and the bad news is the traffic is still flowing through their servers. This time they are tunneling HTTPS traffic over HTTP connection to their server. Details are given below.
This time again we had browsed https://www.google.com, and found that again DNS requests are sent for Nokia/Ovi servers and this time it was “cloud13.xpress.nokia.com”. Up on receiving DNS reply, a HTTP tunnel is eshtablished between Mobile device and their cloud server and HTTPS traffic is tunneled over that HTTP tunnel.
The snapshot given below shows DNS query and HTTP traffic for HTTPS site.

Also HTTP header shown below confirms this info where “x-nokiabrowser-host” parameter informs Nokia server to fetch a perticular HTTPS url and later the content is passed over to mobile device. We are yet to try seeing certificate information in this as it is neither available from Phone nor from packet sniff as was possible previously. I am yet to check how is GET/POST requests to a HTTPS site is handled.
POST / HTTP/1.1 Host: cloud13.xpress.nokia.com Content-Type: application/octet-stream x-nokiabrowser-host: https://www.google.com connection: Keep-Alive accept: */* cache-control: no-cache x-device-id: <removed> Content-Length: 362 Connection: Keep-Alive User-Agent: Nokia302/5.0 (14.78) Profile/MIDP-2.1 Configuration/CLDC-1.1 x-wap-profile: "http://nds1.nds.nokia.com/uaprof/Nokia302r100.xml" ETLV.4J....I...G..L....[OUTPUT-CUT]
I would like to Thank Nokia officials for quickly responding to the issue and getting it fixed on priority. This shows their commitment towards privacy of their mobile customers, much appriciated